Description
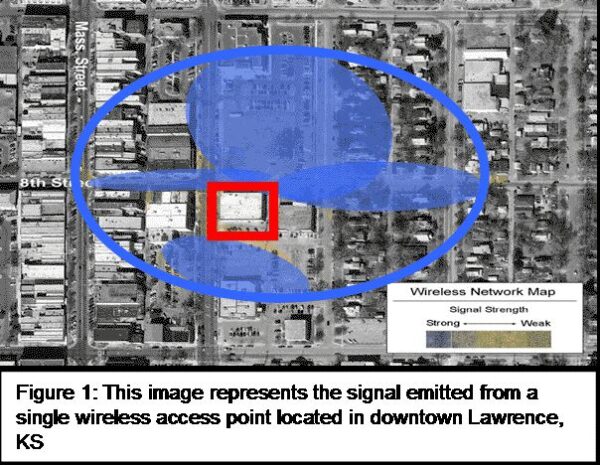
2001 Gartner estimated that “at least 20 percent of enterprises already have rogue WLANs attached to their corporate networks.” Employees can easily hide their rogue access points to wired-side sniffers by simply setting the access point to duplicate the MAC address of
the laptop – an easy and often mandatory configuration for a consumer-grade access point when installed to a home cable or DSL modem. Other rogue deployments or unauthorized uses of wireless LANs can include ad hoc networks. These peer to-peer connections between devices with WLAN cards do not require an access point or any form of authentication from other stations with which it connects. While ad hoc networks can be a convenient feature for
users to transfer files between stations or connect to shared network printers,




Reviews
There are no reviews yet.